
Mailgun Optimize’s Complete Guide to Email Deliverability Best Practices
You'll often hear that the best email in the world has to be opened before it does any good. But an effective email strategy starts with deliverability best practices. It doesn’t matter how good your email or your subject line is if the message never makes it to your subscriber’s inbox.
Email deliverability can be complex and a bit mysterious. But if you fail to focus on it, all your investments in email communication could fall flat. The bottom line? You’ve got to get emails delivered if you want email marketing efforts to deliver results.
Keep in mind, some of the emails you send are much more than marketing promotions. They could contain important information about online orders, password resets, shipping updates, and account creation. You definitely don’t want those messages getting blocked by mailbox providers or landing in the junk mail folder.
The email deliverability experts from Mailgun Optimize are here to help. We’ve put together this comprehensive guide to boost your chances of getting delivered to every contact on your list. In this guide, we’ll cover everything from spam traps and email authentication to email verification and sender reputation.
Let’s get started...
Table of content
-
01
-
02
What is email deliverability? -
03
How is email deliverability measured? - Bounce rate
- Delivery rate
- Inbox placement rate
-
04
What causes email deliverability issues? - Spam traps
- Spam complaints and unsubscribe rates
- Spam scores
- Blocklists
- Email authentication failures
-
05
Understanding email authentication - Sender Policy Framework (SPF)
- DomainKeys Identified Mail (DKIM)
- Domain-based Message Authentication, Reporting and Conformance (DMARC)
- Brand Indicators for Message Identification (BIMI)
-
06
Email deliverability and sender reputation - Domain reputation vs. IP reputation
- How to check your email reputation
-
07
10 best practices to support optimal email deliverability - 1. Warming up your IP and domain
- 2. Following anti-spam and data privacy laws
- 3. Setting up email authentication
- 4. Increasing email engagement
- 5. Verifying email contacts and cleaning your list
- 6. Using a double opt-in
- 7. Never purchasing an email list
- 8. Avoiding spammy behavior
- 9. Monitoring email deliverability metrics
- 10. Conducting a deliverability audit
-
08
How Mailgun Optimize can help
What is email deliverability?
It’s as simple as it sounds, but things can get complex very quickly. Email deliverability focuses on methods that help messages land in the inbox rather than being blocked or filtered into spam folders by mailbox providers.
The mailbox providers or inbox service providers (ISPs), which include Gmail, Outlook, Yahoo Mail, AOL, and Apple Mail, are the main gatekeepers. If they don’t trust you as a sender or think you’re up to something suspicious, they may choose not to deliver your emails (or at least send them to junk).
Mailbox providers want to serve their users, which means prioritizing recipients, not senders. On the one hand, they want to make sure people using their services get all the messages they need and expect. On the other hand, if it can be helped, mailbox providers don’t want to let spam and phishing attempts into anyone’s inbox. Either of these missteps erodes trust among users who may switch to a different email service.
So, to put it plainly, email deliverability involves following a set of best practices that prove you are a responsible sender and not a spammer or a scammer. That often means doing what’s best for your subscribers while helping mailbox providers identify your legitimate messages so they can sort the good from the bad.
How is email deliverability measured?
There are a few metrics that reveal whether your email deliverability is strong or in poor shape. You can use these indicators to determine the overall health of your email program. They include:
- Bounce rate
- Delivery rate
- Inbox placement rate
Let’s take a closer look at each one.
Bounce rate
An email bounces when it fails to be delivered, which could happen for a variety of reasons. There are two different types of email bounces:
1. Hard bounces
A hard bounce occurs when there is a permanent delivery failure, which may indicate a serious email deliverability problem. Namely, it could mean that the receiving email server decided to block your message.
Other reasons for a hard bounce include:
- Fake email addresses
- Typos in email addresses
- Nonexistent domain name in the email address
- Invalid emails from a purchased list
If you have a high number of hard bounces, it could lead to getting blocklisted, which is something we’ll address later. If you have a smaller number of hard bounces, it’s likely related to having some invalid emails. However, it’s important to remove those contacts from your list as soon as possible to protect your reputation as a sender.
Some email service providers (ESPs) will do this for you, automatically adding invalid emails that return a hard bounce to a suppression list.
2. Soft bounces
A soft bounce indicates a temporary email deliverability problem. It’s less serious than a hard bounce but is still something you’ll want to keep an eye on.
Common reasons for soft bounces include:
- The contact’s email inbox is full.
- The size of the email is too large to be delivered.
- The contact’s email server is down/offline.
- Mailbox configuration issues.
You can try re-sending to email addresses that result in soft bounces. But if it continues to happen, those contacts should be removed from your list.
While an ideal bounce rate varies depending on a number of factors, in general, you’ll usually want to keep your bounce rate below 1%. That includes both hard and soft bounces.
Delivery rate
Even though you’ll hear the term thrown around in email marketing circles there’s no such thing as a “deliverability rate.” What those marketers are actually talking about is the delivery rate.
The delivery rate measures the percentage of emails that make it to recipients’ mailboxes. That means any folder: the inbox, spam, promotions tab, etc. It counts any email that didn’t bounce.
So, let’s say you send a campaign to 100,000 email addresses. If 5,000 get blocked, another 5,000 bounce, 10,000 go to spam, and 70,000 land in the inbox, your delivery rate is 80% (not 70%). That’s because even the emails that landed in spam were technically delivered. As long as the message didn’t bounce or get blocked, it counts toward the delivery rate.
You should aim for a delivery rate of 95% or higher. For comparison, users of Sinch Mailgun have an average delivery rate of 97.4%.
Inbox placement rate
A more precise way of measuring email deliverability is to monitor inbox placement. This looks at the percentage of messages that actually made it to the main inbox. So, it excludes anything that’s quarantined to spam or delivered to other folders instead.
In the Mailgun Optimize graphic below, this sender is getting an amazing 97.9% inbox placement rate while just 0.6% of emails are going into spam. The rest are marked “Missed,” which is likely because of invalid addresses that bounced or failed to reach the inbox for another reason.

Besides measuring what happens after emails are sent, you can also predict inbox placement, which gives you a better idea of email deliverability ahead of time. That means you’re able to address deliverability issues before you hit send. Find out more about the inbox placement solutions from Mailgun Optimize.
There are other deliverability metrics you should monitor, such as spam complaints and unsubscribes, but these don’t exactly measure deliverability. Instead, they could cause deliverability issues if they get (and stay) too high.
What causes email deliverability issues?
There are plenty of reasons why an email doesn’t get delivered. But let’s check out some of the biggest email deliverability pitfalls that hurt your chances of landing in the inbox. When your deliverability metrics are looking bleak, this is where to start looking for problems.
Spam traps
If you’ve bought a list, rented one, or scraped the internet to gain contacts, there could be imposter email addresses hiding in your list. That’s because mailbox providers and other entities plant traps to catch potential spammers. And if you built your list in a shady way, you are spamming those people.
Basically, a spam trap is an email address that never was or is no longer connected to a real subscriber, which suggests you’re collecting contacts in a deceptive or illegal manner. There are a few different types of spam traps:
1. Honeypots or pristine spam traps
Pristine spam traps are email addresses made for the express purpose of catching spammers. They are fake contacts hidden around the web. If they end up on your list, it’s a clear sign that you’re a spammer who either purchased contacts or has been scraping the internet for email addresses.
They’re also often called “true traps” or “honeypots” because they attract spammers like bears are attracted to pots of sweet honey. Mailbox providers, cybersecurity firms, and blocklist providers place these fake email addresses where spammers are likely to find them. So, those who try to harvest contact information for spamming end up getting caught when they send to a spam trap.
Honeypots have never been used as a real email address. That means there’s almost no possible way one could end up on your list unless you really are a spammer. In that case, it’s time to clean up your act if you want to improve email deliverability.
2. Recycled spam traps
When someone abandons an old email address, because they leave a job or school or just stop using it, that could become a recycled spam trap.
Mailbox providers sometimes repurpose old email addresses to catch senders who acquire contacts illegitimately. Of course, in this case, it may be that you haven’t removed those inactive contacts from your list yet. So, recycled spam traps aren’t as serious as pristine spam traps. But they can still hurt email deliverability.
If you continue sending emails to a recycled spam trap, this could eventually get you added to a blocklist or cause your emails to land in the junk folder. Plus, if those old email addresses predate GDPR, you could be fined for failing to obtain consent.
3. Typo spam traps
The least offensive spam trap involves common spelling errors and typos in an email address.
For example, maybe a user typed in gnail.com instead of gmail.com when subscribing to your newsletter. Or maybe someone jotted down their contact info at a convention or point of sale and it was tough to read their handwriting. Typo traps may not impact deliverability immediately, but if you don’t clean them up, your bounce rate will increase which will eventually cause problems.
The best way to avoid spam traps is to verify email addresses upon collection, which is a standard feature of Mailgun Optimize’s deliverability suite. You can also try bulk verifications for a large group of contacts to help clean your email list.
Spam complaints and unsubscribe rates
Back in the early 2000s, AOL became the first mailbox provider to give recipients the opportunity to mark emails as spam. Today, the report spam feature is part of every email inbox, and it’s what makes up the complaint rate metric.
A complaint rate that’s under 0.1% is considered acceptable. The industry standard, however, is to have fewer than 0.02% of your messages marked as spam. That is pretty minuscule.
Sometimes recipients mark legitimate emails as spam. They may simply be tired of hearing from you. Maybe you’ve been emailing them a bit too much and they want to unsubscribe. For that reason, make sure there’s an easy and obvious way to let subscribers opt-out of your emails. Losing a few subscribers is way better than a high spam complaint rate (especially when you’re not really spamming).
However, an unsubscribe rate can certainly be too high and have a negative impact on email deliverability. If mailbox providers see that lots of people don’t want to hear from you anymore, that’s a signal that you may be acting like a spammer. It’s not uncommon to see a few unsubscribes with every campaign. But your unsubscribe rate should be no more than a fraction of a percent.
If you start to see an unsubscribe rate near 0.5%, that’s a good time to clean your list to remove inactive subscribers and try to increase email engagement with strong subject lines and compelling email content.
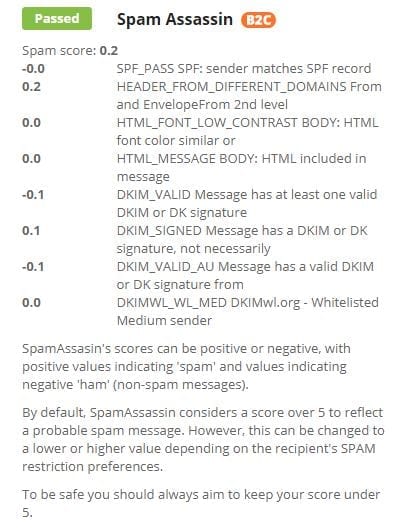
Spam scores
There has to be some sort of tipping point when mailbox providers decide a message qualifies as spam. Mailbox providers and spam filters do this by assigning a score to emails, which essentially rates the likelihood of it being spam.
Different filters and ISPs have proprietary methods for assigning a spam score, but they basically work the same way. There are different spam signals that count against your spam score, and after it crosses a certain threshold, the message gets quarantined. In some cases, doing something right may also bring down your spam score.
One of the most popular spam filters is SpamAssassin, which is an open-source solution from Apache. Its scoring process is pretty straightforward. SpamAssassin conducts hundreds of tests to check for factors such as email authentication protocols, suspicious links, invalid message IDs, missing MIME sections, and spammy terms.
A positive score is applied if the test result indicates a likelihood of spam. A negative score or no score is applied if there’s no sign of spam, or you’re doing things right. All those individual test results are added up to create the spam score. The higher it is, the greater the likelihood of spam.
The default threshold for a SpamAssassin score is “5” with a “10” being the highest. The spam filter Barracuda has a similar scoring system. But keep in mind that mailbox providers and system admins can adjust the settings to be higher or lower as well as choose the specific checks they want to run.
When Email on Acid runs a SpamAssassin test during deliverability checks, we use the default score of “5” to provide a pass/fail result on that particular email.
In addition to the spam testing built into Email on Acid’s Campaign Precheck, Mailgun Optimize users can conduct inbox placement tests using a seed list to get an even more comprehensive report on email deliverability. In the sample report below, you’ll notice that 100% of emails went to spam for some mailbox providers (Outlook and Hotmail). That’s an indication that your domain or IP may be blocklisted by those email clients.

Blocklists
A blocklist (formerly referred to as a blacklist) is a list you definitely don’t want to be on. But it does happen, even to legitimate senders and well-meaning email marketers. Blocklists are databases of sender domains or IP addresses assumed to be transmitting spam. If you’re on the list, your emails may not be delivered to any mailbox provider using that blocklist.
There are two main types of blocklists:
- Domain-Name System Based Blocklists (DNSBLs): A list of blocked sending domains
- Real-Time Blocklist (RBLs): Catches offending IP addresses in real time
Vendors like Barracuda, SpamCop and Spamhaus operate blocklists. Plus, mailbox providers like Microsoft Outlook have their own internal blocklists as well. The impact that being blocklisted has on deliverability will depend on the blocklist and how widely it’s used. However, landing on smaller blocklists is still a sign that you’ve got potential email deliverability issues.
It’s worth noting that, even if you end up on blocklist, it’s still up to the receiving mail system to decide if your messages get delivered or blocked. Here’s how Spamhaus explains it:
“Spamhaus does not tell a 3rd-party mail system what to do with an item of email. The 3rd-party mail system asks Spamhaus for an opinion and Spamhaus responds to that request with its opinion. In effect the receiving mail server asks the Spamhaus DNSBL ‘Does this Sender's IP Address exist on the Spamhaus database?’”
Here’s a diagram of how that works:

How do senders get blocklisted?
You could end up on a blocklist for a bunch of different reasons. They include:
- Spam traps in your contact list
- Too many spam complaints
- A sudden, unnatural jump in the size of your list
- Mail server configuration issues
- Failing to honor unsubscribe requests
There are plenty of other factors, some technical and some policy related. Each blocklist has its own set of criteria, which is why the most effective way to avoid being blocklisted is to follow email deliverability best practices, watch out for technical issues, and act like a respectable, responsible sender
How do you get removed from blocklists?
There are a lot of blocklists around the world, and there’s a good chance your sending domain is listed on at least one or two of them. That may not be a major issue. But it is important to stay off the most used blocklists.
If you do end up on a major blocklist and your email deliverability is impacted, you’ll often receive a notification that indicates the next steps you can take for potential removal.
Many blocklist providers have a defined self-service path to getting delisted. This usually involves sending them your contact information and any comments as to the possible reason for the block. Others will provide a case-specific email address and subject line.
For major DNSBLs like Spamhaus and Spamcop, you can request specifics about the offending traffic and find out why the blocklisting occurred. This helps you target and fix the issue. It will also be helpful when you explain what you’ve done to remediate the problem that got you on the blocklist.
Get more information on blocklist removal from our friends at Mailgun.
Email authentication failures
One of the biggest threats to email security is phishing, which includes a tactic known as brand spoofing. This is when a bad actor tries to impersonate a recognizable brand using fake messages that appear real at first glance. The fake email sends people to a fake (but convincing) landing page where scammers collect sensitive information.
Spoofing can hurt your brand reputation, and mailbox providers want to block these emails to protect recipients. That’s where email authentication protocols and specifications come in. Here’s how deliverability expert Nick Schafer describes it:
“Mailbox providers need ways to identify who a sender really is. Without email authentication, it’s hard to tell where email traffic is really coming from. What authentication does for senders is it makes it possible for them to say, ‘This message is from us, it’s our email traffic, and we’re allowed to do this.’”
~ Nick Schafer, Manager of Deliverability & Compliance, Mailgun
Email authentication includes the use of:
- SPF or Sender Policy Framework
- DKIM or DomainKeys Identified Mail
- DMARC or Domain-based Message Authentication, Reporting, and Conformance
Receiving mail servers look for these authentication factors before deciding whether to deliver, block, or quarantine your emails. While failing authentication doesn’t guarantee anything, it certainly increases the likelihood your message won’t be delivered to the inbox.
Emails often fail authentication and get blocked or quarantined when they come from an impersonator. But legitimate messages could also suffer email deliverability issues if authentication protocols are missing or if records are improperly configured.

Understanding email authentication
Email authentication is one of the more technical areas of deliverability. It involves the use of DNS TXT records, which need to be set up on your sending domain servers, and specific information that’s included in the email header. When a receiving mail server processes a new message, it takes header information and uses the DNS TXT records to verify the authenticity of the sender.
Enforcing email authentication supports email deliverability because it gives mailbox providers a strong signal that your messages are safe and legit.
Sender Policy Framework (SPF)
No, this isn’t sunblock. An SPF record is a list of domains and IP addresses that are approved to send mail on your behalf. When receiving mail servers try to authenticate a message, they match up the sending domain or IP with the list published on your DNS.
SPF is sort of like a bouncer at a VIP event. If you’re on the list you get into the inbox, if you’re not... you probably don’t.
A domain can only have one SPF record. However, it’s totally possible to have more than 10 approved IPs. Using an “include” parameter in the SPF record allows senders to add long lists of IP addresses. One well-known drawback of SPF authentication is that it breaks when an email is forwarded. That’s because the email is now being sent from a new IP, which is not listed on the SPF record.
DomainKeys Identified Mail (DKIM)
DKIM authentication involves encrypted keys that help verify a sender’s identity. At this VIP event, instead of being on the list, you need to give the bouncer (aka mailbox provider) the secret password to get inside the inbox party
When you set up DKIM, there is a public key that’s published in the DNS record and a private/encrypted key that’s sent with the email. That private key is also known as a “digital signature,” which should be unique to the sender.
The receiving mail server pairs up the encrypted key with the public key to authenticate the message. If the keys don’t match up, email deliverability issues are more likely.
Domain-based Message Authentication, Reporting and Conformance (DMARC)
The email industry introduced DMARC to help stop spoofing by combining the powers of DKIM and SPF while creating a policy that informs mailbox providers what to do with messages that fail authentication.
Another benefit of DMARC is that it provides regular reporting on your email traffic. This lets you see who is sending email on your behalf, makes it easier to catch spoofing, and helps identify potential email deliverability issues.
When a sender implements DMARC, receiving mail servers will check for both SPF and DKIM alignment. Then it checks the DMARC DNS record to find the policy for handling authentication failures.
There are three possible DMARC policies:
p=reject: This means authentication failures should be blockedp=quarantine: This means authentication failures should go to spamp=none: This means messages that fail authentication could still land in the inbox
A p=none policy leaves email deliverability up to the mailbox providers. But, trust us, they’d rather have your help deciding what to do with emails that fail authentication. That’s why they created DMARC in the first place.
The problem is that too many senders set up relaxed DMARC policies, which lets them get reports but not much else. The only way to effectively use DMARC to thwart email spoofing is to enforce a policy set to p=reject or p=quarantine.
Brand Indicators for Message Identification (BIMI)

BIMI is like a fun bonus for senders who are kicking butt at email authentication. If you’re doing it right, you qualify for displaying a branded logo in the inbox. (And what brand doesn’t want their logo in more places?)
In order to be “BIMI-ready,” you must set up DMARC with DKIM and SPF. Most importantly, your DMARC policy must be set to p=reject or p=quarantine. If you’re using p=none, you don’t qualify for a BIMI logo.
BIMI doesn’t directly impact email deliverability. However, there’s research suggesting a branded inbox experience increases subscriber engagement, which is definitely good for supporting deliverability. Plus, if you have a BIMI logo, it’s a strong sign that you have a good sender reputation.

Email deliverability and sender reputation
While individual email messages receive spam scores, sender reputation involves rating the trustworthiness (or spamminess) of different domains and IP addresses. It’s a lot like a credit score for email marketers. Sender reputation (or email reputation) is a major consideration in email deliverability.
Email reputation is measured by evaluating the behaviors of either a particular sending domain or a specific IP address. So, what’s the difference?
Domain reputation vs. IP reputation
Domain reputation is connected to the domain used to send email from your organization. This may be your main domain (example.com), or certain subdomains (mail.example.com, marketing.example.com, etc.).
Using subdomains for different emailing purposes can help protect your domain reputation. This way, if marketing promotions are sent from a separate subdomain, and people start complaining about spam, it won’t impact email deliverability for the domain used to send transactional messages.
Domain reputation is connected to brand reputation. If you’re a well-known, reputable brand, mailbox providers assume recipients want and expect your messages. So, they’re more likely to get delivered.
IP reputation measures the trustworthiness of unique IP addresses where email originates. It relies on factors such as bounce rates, spam complaints, message content, and other factors traced back to the sending IP. You can always start fresh with a new IP, but you’ll also need to warm up that IP address and build a better email reputation from scratch.
The problem is that some senders use shared IP addresses while others have a dedicated IP address for sending email. On a shared IP, you also share the reputation of other senders.
Dedicated IPs are normally only used by high-volume senders (more than 100,000 emails per month). If you’re using a traditional ESP, it’s likely that you are on a shared IP. That’s why Mailgun deliverability expert Nick Schafer thinks most mailbox providers lean more towards measuring domain reputation.
“Shared networks are a common thing, and it’s not in a mailbox provider’s best interest to block email traffic that recipients need and want to see in their inboxes. Domain reputation is usually a better indicator of good and bad senders.”
~ Nick Schafer, Manager of Deliverability & Compliance, Mailgun
However, Nick adds that IP reputation is still a factor you should consider. That’s because he knows email clients like Micrsoft Outlook still use IPs for email reputation scoring, which means it could be quite important for B2B email deliverability.
Here’s how Google Postmaster Tools defines different IP and domain reputations:
- Bad: A history of sending a high volume of spam. Mail coming from this entity will almost always be rejected at connection time or marked as spam.
- Low: Known to send a considerable volume of spam regularly, and mail from this sender will likely be marked as spam.
- Medium/Fair: Known to send good mail, but has occasionally sent a low volume of spam. Most of the email from this entity will have a fair deliverability rate, except when there’s a notable increase in spam levels.
- High: Has a good track record of a very low spam rate, and complies with Gmail's sender guidelines. Mail will rarely be marked by the spam filter.
So, maintaining a strong email reputation seems fairly simple. Don’t do spammy things, right? Still, it is important to monitor and maintain a good sender reputation to maximize email deliverability.
With Mailgun Optimize, you can integrate Postmaster Tools as well as Micrsoft SNDS, which helps you monitor your sender reputation with Outlook.
How to check your email reputation
Different mailbox providers have unique ways of scoring a sender’s reputation. There are some services that help you check sender reputation by providing an overall rating. But you can also use tools provided by the mailbox providers themselves.
For example, Google Postmaster Tools can help you check your reputation with Gmail. Microsoft SNDS is helpful for monitoring deliverability to Outlook addresses. The MXToolbox SuperTool is super useful because it checks for a variety of factors that impact sender reputation.
Talos from Cisco has a domain and IP reputation checker that shows whether you’re trusted or not. There’s also the BarracudaCentral, which lets you look up your reputation with the Barracuda spam filter and blocklist.
If you discover you need to improve your sender reputation, Mailgun Optimize can provide dedicated email deliverability specialists who can guide and consult you along the way. When you opt for Deliverability Services, our dedicated Technical Account Managers can help you create a custom strategy along with proactive reputation monitoring.

10 best practices to support optimal email deliverability
Maybe you’ve noticed a bit of a theme running through this guide...
Email deliverability best practices = Doing the right thing.
But just exactly what are the right things to do in support of deliverability? Here’s our top 10 list of email deliverability best practices:
1. Warming up your IP and domain
When an organization starts using a brand new, dedicated IP address for sending email, that IP has no history with mailbox providers. So, it needs to start building up a sender reputation. This is kind of like not having a credit score until you get a credit card or take out a loan.
If you’re a high-volume sender using a new IP or sending domain, it may look suspicious if a ton of emails suddenly start coming from those sources. The domain and dedicated IP warm-up process helps with this. Failing to warm up a new IP is likely to hurt deliverability as ISPs block or quarantine the messages that they’re unsure about.
NOTE: This is less of a problem with shared IPs since they already have an email reputation with mailbox providers.
The warm-up process involves starting to send out emails slowly and gradually increasing the volume and frequency. This gives the mailbox providers and ISPs a chance to review the content of your messages and see how recipients respond. If they open and engage, you’re good. If they ignore, delete, or mark emails as spam, you're not so good.
Imagine you’re trying to get a “date” with a mailbox provider. The IP warmup process is sort of like making a good first impression, taking it slowly, and meeting their friends before you make your move.
You can follow a manual warmup process, or your ESP may offer an automated IP warmup service for customers using a dedicated IP.
2. Following anti-spam and data privacy laws
Breaking the law is probably the easiest way to ruin your email reputation (not to mention the potential fines). Data privacy continues to be a major issue for consumers and businesses around the world. Anyone with an email list is handling personally identifiable information (PII) because email addresses are PII.
To maintain a strong sender reputation and support email deliverability, make sure you follow these laws:
CAN-SPAM
CAN-SPAM stands for “Controlling the Assault of Non-Solicited Pornography and Marketing.” The United States’ anti-spam law has been around since 2003. It was one of the first of its kind, and it’s not without its critics or controversy. Namely, a lot of privacy advocates and others in the email industry felt it didn’t go far enough.
However, it does establish some specific rules for sending commercial emails. The U.S. Federal Trade Commission (FTC) lists these main CAN-SPAM requirements:
- Don’t use false or misleading email header information.
- Don’t use deceptive subject lines.
- Identify messages as an advertisement.
- Tell recipients where you are located.
- Tell recipients how to opt out of receiving your emails.
- Honor opt-out requests promptly (within 10 business days)
- Monitor what others are doing on your behalf (third-party solution providers)
Find out more about CAN-SPAM compliance for email marketers.
CASL
The Canadian Anti-Spam Law (CASL) is considered to be a bit tougher on spam than the U.S. version. (So, I guess Canadian politeness doesn’t apply to spammers).
One thing that separates CASL from CAN-SPAM is that Canada’s law requires both an opt-in process and a way to opt-out. The U.S. law only requires a way to unsubscribe, which some feel gives senders a license to spam. CASL also applies to a wider variety of electronic messaging, whereas CAN-SPAM applies to email and some text messages.
Find out more about CASL compliance for email marketers.
GDPR
The European Union’s General Data Protection Regulation (GDPR) was the data privacy legislation that rocked the world when it became law in 2018. It’s still shaking things up, and it’s become the standard for new consumer privacy legislation.
While complying with GDPR is serious business, it shouldn’t be a huge concern for senders who are already following best practices and acting responsibly.
These are the seven key principles of GDPR:
- Lawfulness, fairness, and transparency: Have a lawful/appropriate reason for collecting, storing, and processing personal data. This principle includes obtaining consent as well as outlining how and why data is used in a readily available company privacy policy.
- Purpose limitation: Establish limits on how personal data is used and communicate those limits in the privacy policy.
- Data minimization: Collect the smallest amount of personal data required. Don’t acquire or store sensitive data you don’t need.
- Accuracy: Take steps to make sure personal data is correct, complete, and up to date.
- Storage limitation: Be prepared to justify the length of time personal data is stored and anonymize data you don’t actively use.
- Integrity and confidentiality: Have security measures in place to protect sensitive data and personal information from bad actors.
- Accountability: Have a system of records in place that proves you are following GDPR.
An important aspect of GDPR is the ability for consumers to ask for all the data collected about them and to have it deleted upon request. These are known as data subject access requests (DSARs). And that’s one reason why meticulous digital record-keeping is crucial when complying with the EU’s privacy law.
GDPR should be followed even if you aren’t doing business in Europe. Even If you’re a small business, it’s tough to tell whether someone on your list is in the EU or not.
Find out more about GDPR compliance for email marketers
CCPA
The California Consumer Privacy Act (CCPA) is a state law that came about not long after GDPR, and it follows many similar principles and rules.
While CCPA only applies to consumers residing in California, it has become a sort of de-facto law of the land in the U.S. That’s because (as of this writing) there’s still no federal law that’s considered a GDPR-equivalent.
The differences between CCPA and GDPR are in the details. For example, while GDPR protects “data subjects” CCPA protects “consumers.” In that case, the GDPR law is a bit broader.
The CCPA also protects household and device-specific data, and it includes a provision requiring the ability to opt-out of having personal data sold to third parties, which GDPR does not. On the other hand, GDPR is stricter about getting parental consent for processing data of those under the age of 16 (or 13 in some regions).
Find out more about CCPA compliance for email marketers.
And more to come...
Following the launch of CCPA, other states followed suit, drafting their own privacy laws. However, a comprehensive federal U.S. privacy law could be on the way. That could make things a lot simpler and more consistent.
The largely bi-partisan American Data Privacy and Protection Act (ADPPA) is working its way through congress, but it could take a while to become law.
Outside of the EU, plenty of other countries have their own data privacy laws, which you should follow if you do business and send email in those nations. However, in most cases, being GDPR compliant keeps you covered for other laws. (Please consult your own legal experts for official advice.)
Senders may also need to consider things such as PCI compliance for credit card processing or HIPAA for healthcare data privacy in email.
The connection between email deliverability and compliance with privacy laws should be clear. Senders who respect those laws and guidelines are putting their subscribers first, and that tends to mean you are following many email deliverability best practices.
3. Setting up email authentication
Email authentication protocols aren’t part of any laws, but they would be if mailbox providers ran the world. We’ve already discussed the importance of email authentication to deliverability. At a minimum, you should set up SPF and DKIM authentication.
While ESPs can often help with setting up email authentication protocols, you’ll need to be sure your DNS records are correct. That includes adding your ESP to your SPF record.
Where you can really make a difference is with DMARC, including an enforcement policy set to p=reject or p=quarantine. That will go a long way towards protecting your reputation as a sender.
If DMARC sounds too technical for you and your team, there are vendors out there who specialize in helping you implement everything. They include:
4. Increasing email engagement
It almost sounds too simple, but it’s 100% true: sending awesome email campaigns will support better email deliverability.
When mailbox providers see that recipients are opening and engaging with your messages, they’ll know people want to receive what you’re sending. That means Gmail, Apple Mail, Outlook, and the rest of the gang are more likely to make sure your emails land in the inbox where people will find them.
So, create email campaigns that people love. When you strategize, write, design, and develop emails, ask yourself what your subscribers want and how you can surprise and delight them. Make it so that everyone on your list anticipates your next email.
Check out our free, on-demand webinar on improving email engagement to get some great ideas.
5. Verifying email contacts and cleaning your list
Of course, there will always be some party poopers on your list. So, clean that crap up!
You should take the time to conduct some email list hygiene at least twice a year. That means removing inactive subscribers and invalid/outdated contacts. That will help keep your email engagement metrics looking good.
Maintain a cleaner list throughout the year by verifying email addresses when people sign up or fill out a form on your site. Check out some email list cleaning best practices to learn more. Mailgun Optimize’s email verification features are an excellent tool to help you scrub your list and keep it clean. Check out Mailgun Validate for a dedicated email verification solution, including a validation API you can integrate into your site, online forms, and applications.
6. Using a double opt-in
The best way to make sure new subscribers are valid and actually want to hear from your brand is to implement a double opt-in process. In essence, this involves double-checking that a new contact truly wanted to subscribe.
Here’s how a double opt-in process works:
- A new contact fills out a form or subscribes to your email list.
- You let them know to check their inbox to confirm the subscription.
- You send them a follow-up email asking them to click and confirm.
- If the contact clicks to confirm, you add them to your list.
- If the contact does not confirm, they haven’t officially opted in yet (so you don’t add them).
Now, you’re probably thinking, “If I do that, I’m not going to grow my list nearly as fast because there are going to be a bunch of people who miss or ignore that confirmation email, man!”
That’s probably true. But if the contact doesn’t open and engage with your confirmation email, how likely are they to open and engage with future campaigns? It’s more likely that they’ll just become dead weight that you’ll need to remove from your list down the road.
Don’t forget... good email engagement supports better email deliverability.
When implementing a double opt-in process, make sure the entire flow is compelling and convincing. Confirmation emails should have strong subject lines and you can A/B test those emails to optimize them for conversions.
Use the fear of missing out (FOMO) to move new contacts along in the double opt-in process: “You don’t want to miss what will be sharing with you in coming months.” Or consider offering an incentive such as a discount code on the Thank You page after people opt in.
7. Never purchasing an email list
Just don’t do it. It’s a bad idea. It won’t work... at least not for long. And it could get you in some serious trouble (spam traps, blocklists, privacy violation fines, etc.).
Sure, your list gets a lot bigger when you pay for it. But those contacts didn’t want to hear from you. That means they’re not interested, they’re not going to convert, and they’re going to mark your emails as spam (which they should).
If you need some lessons in how to do things the right way, check out our article on the timeless lessons in Seth Godin’s book, “Permission Marketing.”
Bottom line: purchasing lists will be bad for email deliverability. And in most cases, your email service provider (ESP) will prevent you from using a purchased list anyway.
8. Avoiding spammy behavior
They say that if it looks like a duck, waddles like a duck, and quacks like a duck... it’s not a goose or a chicken. (Hint: It’s probably a duck). The same thing goes for email spam and spammers.
An excellent email deliverability best practice is to ask yourself, “What would a spammer do?” Then, do not do those things.
While occasionally using ALL CAPs or exclamation points probably won’t get you sent to the spam folder, you shouldn’t overdo it either. (It’s also just kind of obnoxious, anyways.) HubSpot has a list of hundreds of industry-specific words and phrases you may want to avoid.
Spammers often use image-only emails, have poor grammar and spelling, use lots of symbols, and use deceptive text in hyperlinks. Remember that a spam score is being applied to every campaign you send. So, don’t act like a spammer and your emails won’t look like spam. It’s that simple.
9. Monitoring email deliverability metrics
We all love benchmarks, but the most important email deliverability benchmark is where you are now. Then, unless you’re perfect, set a goal for improving deliverability metrics.
Look at bounce rates, delivery rates, and inbox placement for individual campaigns as well as your entire email program. How do transactional emails compare to marketing emails and newsletters? Are certain segments of your list more engaged than others?
Keep an eye out for changes in email analytics that may indicate deliverability problems. And make sure engagement is something you consider as you measure email deliverability.

Deliverability Monitoring from Mailgun Optimize helps you stay ahead of those problems before they negatively impact your email program. It includes a dashboard of deliverability metrics along with ongoing monitoring for blocklists and spam traps.
10. Conducting a deliverability audit
If you really want to dig deep into email deliverability, there’s no better way to explore it than with a full-blown audit. This can and should be part of a big-picture email marketing audit. However, you could also choose to focus solely on deliverability.
Our pals at Sinch Mailgun have an in-depth guide to conducting an email deliverability audit. It includes tasks such as evaluating email infrastructure, verifying email authentication, conducting list hygiene, and assessing your sender reputation.
You can decide how technical and complex your email deliverability audit should be. Most importantly, you’ll need benchmarks from the previous year (or quarter) so you can measure improvements and catch potential problems.
After you complete your audit, create a list of action items so that you have a clear plan for improving and maintaining email deliverability moving forward. Some of those items, like list cleaning, can be addressed immediately. Others, like improving your sender reputation, will take more time and dedication.
How Mailgun Optimize can help
Mailgun Optimize is a complete email deliverability suite including tools and insights to help email marketers get the most out of every campaign and help every sender make sure important messages land in customer inboxes.
Mailgun Optimize is built on reliable infrastructure from Sinch Mailgun, but you can use any ESP and still take advantage of all the tool's features and benefits.
Mailgun Optimize offers you the ability to proactively monitor, manage, and optimize your program and your strategy. With Mailgun Optimize, you can:
- Quickly clean up your email list to reduce bounce rates.
- Ensure that every new email address you add to your mailing list is valid.
- Seed test your emails to ensure they’ll land in the inbox and not the spam folder.
- See exactly where they’ll land in Gmail and other mailboxes with tabs.
- Preview campaigns across the most popular devices and email clients.
- Monitor IP blocklists so you can take action immediately.
- Identify and avoid spam traps in your email lists.
- And a lot more – we’re bringing you more great features soon!
Get started with Mailgun Optimize today and grab control of your brand’s email deliverability. Contact us to set up a custom demo. Learn more about how Mailgun Optimize works and how it can help.
EMAIL DELIVERABILITY DOESN’T HAVE TO BE A MYSTERY
A lot can happen on the way to your customers’ inboxes. Wondering if your emails will land in spam, why a major mailbox provider is rejecting messages, or why bounce rates are climbing? Mailgun Optimize can get you those answers. It’s a complete email deliverability suite that helps you stop wondering and start improving.





