Email Deliverability
What DMARC Policy Should Senders Use in 2025?

They say honesty is the best policy. Well, if we are being honest, a lot of email senders are not using the best DMARC policy heading into 2025 – at least that’s according to results from a recent industry survey.
When Google and Yahoo announced new requirements for bulk senders this year, there was a big focus on using email authentication protocols. That includes:
- SPF (Sender Policy Framework)
- DKIM (Domain-keys Identified Mail)
- DMARC (Domain-based Message Authentication, Reporting and Conformance)
As it now stands, every sender needs to be using SPF and DKIM, and bulk senders need to implement DMARC with a minimum policy of p=none. Fail to do so and you may not be able to reach Gmail and Yahoo Mail contacts. Encouraging more senders to adopt DMARC has been a top priority for major mailbox providers. This new requirement pushes senders in that direction, and it seems to be working.
Sinch Mailgun’s new report, State of email deliverability 2025, found an 11% increase DMARC usage compared to its previous report. The problem is, a lot of senders only want to do the bare minimum to meet the new requirements. Unfortunately, that means they’re not getting the most out of DMARC.
What is DMARC and what does it do?
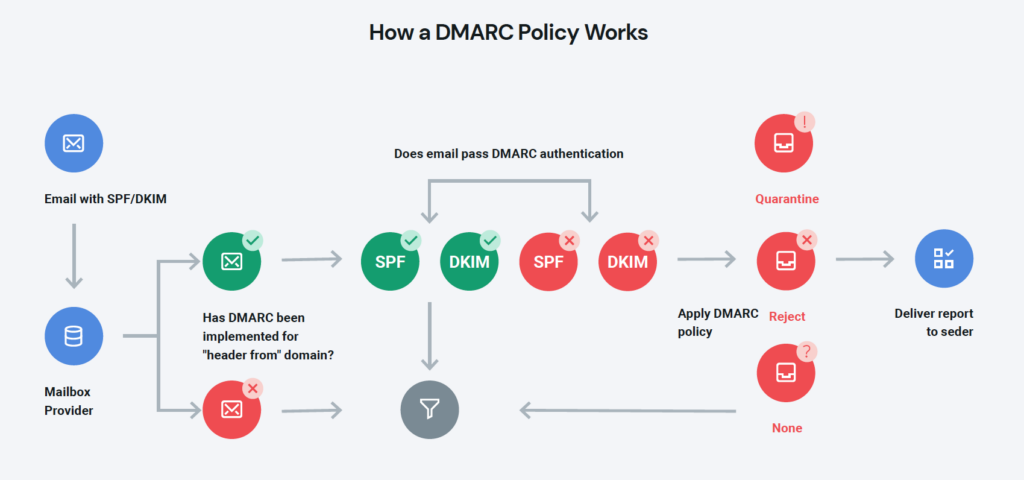
Before we get too far, let’s review how DMARC works alongside other email authentication methods (SPF and DKIM).
When used together, these three DNS TXT records are an effective way to stop email spoofing. That’s because they help mailbox providers (like Gmail and Yahoo) verify the identity of a sender before accepting or rejecting a message.
The main purpose of DMARC is to check for both SPF and DKIM alignment and then advise mailbox providers on what to do with messages that fail authentication.
This protects sending domains from unauthorized use while making it easier for receiving mail servers to verify the identity of the sender. That’s why DMARC helps prevent phishing, business email compromises (BECs), and other email scams.
How DMARC works with SPF and DKIM
SPF and DMARC check for different things. Here’s a quick explanation of how they work:
- SPF is a list of hostnames and IP addresses published on your DNS that are approved to send mail for your domain. For example, this may include a subdomain used for sending email or a shared IP your ESP has added you to.
- DKIM verifies the identity of a sender using an encrypted digital signature or private key that matches a public key on a sending domain’s DNS. DKIM also ensures messages are not altered during transit.
DMARC combines the powers of SPF and DKIM into the most effective way to thwart email phishing.
What is a DMARC policy?
After finding out whether SPF and DKIM pass or fail, a DMARC policy informs mailbox providers as to how messages should be filtered when they fail authentication. Email authentication failures may also be described as SPF or DKIM not being aligned.
Senders have three DMARC policy options:
p=none– This DMARC policy tells mailbox providers not to do anything with messages that fail authentication. It means potentially malicious email spoofing a domain could land in the inbox.p=quarantine– This DMARC policy tells mailbox providers they should filter messages that fail authentication into the spam or junk folder, preventing them from reaching the inbox.p=reject– This DMARC policy tells mailbox provider not to accept any messages that fail authentication. Failures are blocked from reaching any folder.
DMARC also provides regular reporting to senders on authentication failures and who is attempting to send mail on behalf of their domain. These reports are available with a p=none policy. However, a DMARC policy of none does nothing to make the inbox safer. Sinch Mailgun deliverability experts explain exactly why in the video below:
In an ideal world, you’d only use p=none while you set up and test DMARC implementation. Then, you’d move to a DMARC policy of quarantine or reject to actually enforce the specification. A policy of none does nothing to protect the inbox from bad actors. Protecting their users by making the inbox safer was one of Google and Yahoo’s main objectives. So, why did they choose to require only a p=none DMARC policy? We’ll get to that. First, let’s check out some stats.
Statistics on DMARC policies in 2024
When Sinch Mailgun surveyed senders for its latest deliverability report, it took a closer look at both how senders responded to the new requirements (aka Yahoogle) as well as trends in email authentication practices among senders across the globe.
Among senders who made changes to their email programs to comply with new bulk sender requirements, nearly 80% updated their email authentication protocols. Mailgun also found high awareness and adoption rates for SPF and DKIM with more than 66% of all senders knowing they used both protocols while 25% were unsure and the rest used one or the other.
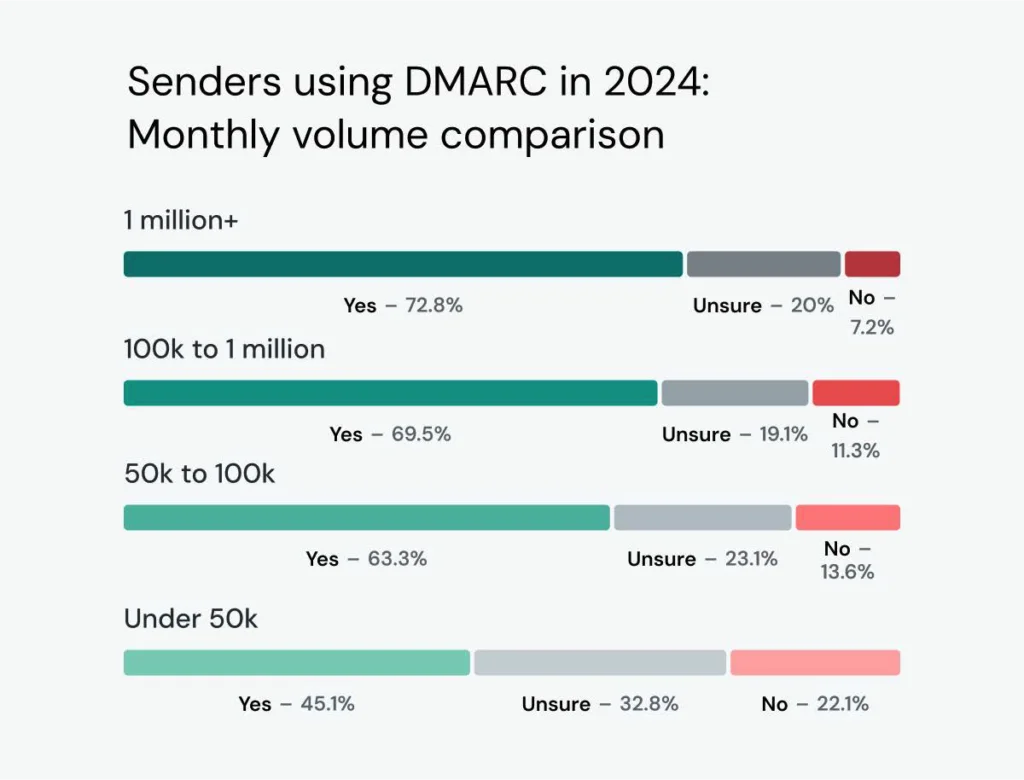
DMARC adoption is not quite as strong, but there were definite improvements from Mailgun’s 2023 findings. Results show overall DMARC adoptions increased from less than 43% in 2023 to nearly 54% in 2024 with a notable decrease in the percentage of senders who were unsure about DMARC usage.
Of course, smaller senders may not need to comply with this new rule. While DMARC is highly recommended for all senders, it’s only required for bulk senders with daily volumes around 5,000 messages. When Mailgun broke down DMARC adoption by send volume, results show around 70% of higher volume senders use DMARC.
Which DMARC policies are senders using?
Sinch Mailgun’s State of email deliverability 2025 found that p=none is the most common DMARC policy among all senders. While nearly 23% of senders used p=none in 2023, almost 32% were using the policy in 2024. It would appear that a lot of the growth in DMARC adoption came in that area.
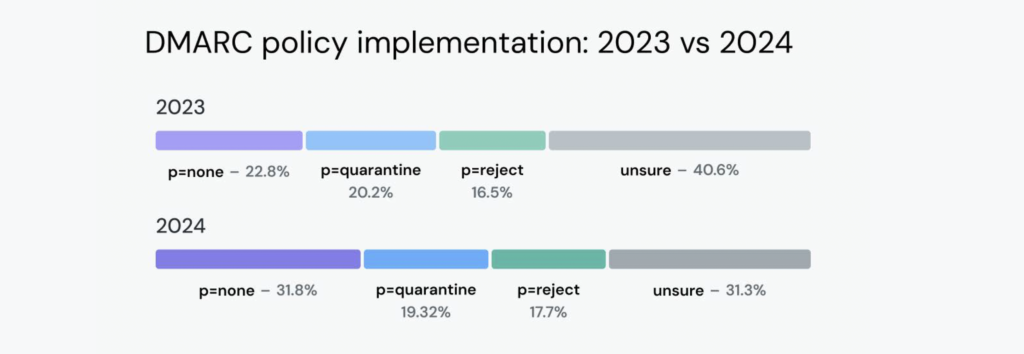
So, are all of these senders just in a testing phase after setting up DMARC for the first time? Mailgun’s survey results do not make it look that way.
Among those using a DMARC policy of p=none, a combined 25% say they plan to begin enforcing DMARC with a stronger policy soon. However, nearly 75% of senders using a DMARC policy of none have no plans to update to quarantine or reject any time soon.
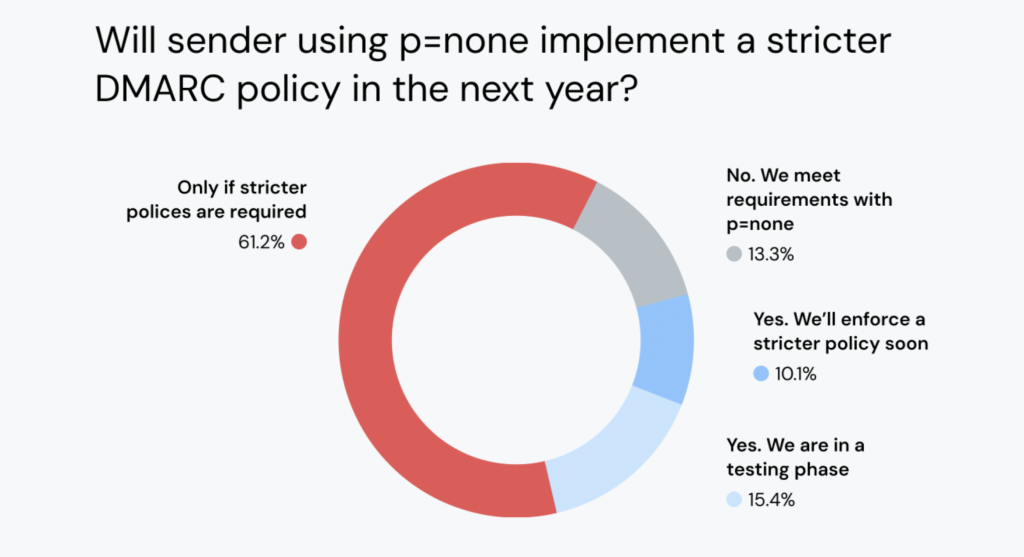
More than 61% of senders say they’ll only start enforcing DMARC if mailbox providers make it a requirement. The reality is — that’s exactly what’s going to happen sooner or later.
What Google and Yahoo want for DMARC policies in 2025
The truth is, the DMARC with p=none requirement is only a first step. Mailbox providers just wanted more senders to start implementing DMARC. Once those records are in place, it is very likely that a policy of either p=quarantine or p=reject will be required in the near future (at least for bulk email senders).
In a webinar with Sinch Mailgun, Marcel Becker of Yahoo confirmed this approach saying:
“The end goal is ideally a policy of p=reject. That’s what DMARC is for. Ensuring that your domain cannot be spoofed and protecting our mutual customers from abuse.”

For more insights straight from Gmail and Yahoo, get key takeaways from Mailgun’s talk with Marcel Becker and Anu Yamunan who is the Director of Product for Anti-Abuse & Safety at Google. You can also watch an Email Camp 2024 panel session with Marcel as well as Google’s Dan Givol.
To be clear… a p=none policy is the minimum requirement. Mailbox providers would much rather have senders enforcing DMARC with a stronger policy.
Want to stay one step ahead of the game? Start enforcing a stronger DMARC policy of quarantine or reject now. It’s worth the time and effort, and not just because it will eventually be required.
The benefits of enforcing a stronger DMARC policy
Some senders hesitate to enforce strict DMARC policies due to fears it may hurt email deliverability. While an incorrectly configured DMARC record or other authentication issues may cause deliverability problems, the truth is that email authentication can lead to better deliverability.
The use of email authentication is a strong signal to mailbox providers that you are a responsible and reliable sender When you’ve got a good email reputation, you are less likely to get blocklisted, less likely to get filtered into the junk folder, and more likely to land in the inbox.
Enforcing a strong DMARC policy is a clear signal that you are working to do the right thing. It protects your reputation as an email sender because it makes it easier for mailbox providers to identify your messages as legitimate and messages from spammers and scammers as malicious.
DMARC benefits for mailbox providers
All major mailbox providers support DMARC. That includes Gmail, Outlook, Yahoo, Apple Mail, and AOL. And as we see with Gmail and Yahoo, it’s important enough to make it a requirement.
For mailbox providers, DMARC provides information about how to filter messages that fail authentication. This is what your domain’s DMARC policy does. When mailbox providers are unclear about how to handle unauthenticated messages, they may lean toward delivering them. That’s because their users would be more upset about not receiving real emails than dealing with spam. This is one reason why potentially dangerous emails sometimes sneak through.
DMARC benefits for email users
For email recipients, DMARC makes the inbox a safer place because it prevents malicious phishing attempts and brand spoofing emails from getting delivered. Specifically, it stops emails with forged information in the “from” field of an email header.
That means consumers have less to worry about when, for example, they open a transactional email from a brand they do business with regularly. Their inbox can be used for important customer communications. Email is a common and popular way for people to connect with brands. Mailgun’s Email and the customer experience report found that around 3/4ths of consumers prefer email for both transactional and promotional messages.
DMARC benefits for senders and email marketers
For email senders, DMARC helps protect brand reputation and also provides valuable reports on the IP addresses that are sending mail on behalf of your domain. This lets you monitor for email spoofing and find out if legitimate emails are encountering authentication issues that impact deliverability. You can set up DMARC so that you get daily reports from servers receiving any emails claiming to be from you.
But more importantly, stronger email authentication helps maintain the integrity of the email channel because it keeps bad actors out of the inbox. It ensures that email continues to be a reliable and useful way to connect.
Try imagining a world in which you could no longer use emails to reach your subscribers, customers, and prospects. Both email senders and mailbox providers want people to keep using email. That’s why Marcel Becker called them “our mutual customers.” Enforcing a DMARC policy isn’t just a good idea, it should be a responsibility. That’s why mailbox providers like Gmail and Yahoo are likely to make p=reject mandatory in the future.
BIMI: The bonus benefit
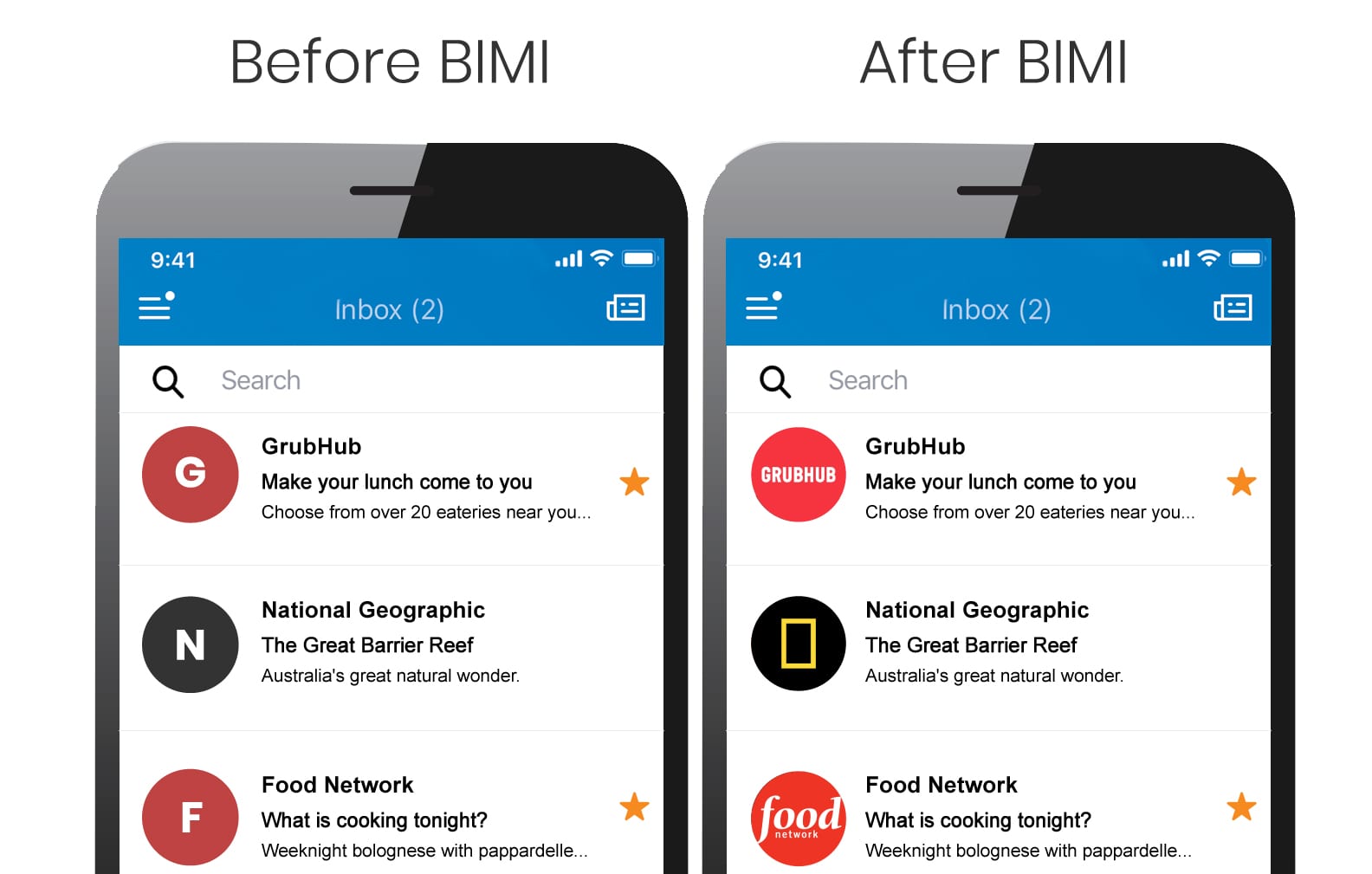
Another potential benefit of a strong DMARC policy is eligibility to have a certified logo show up on your marketing and transactional emails. This is made possible through a specification known as Brand Indicators for Message Idenfitication (BIMI).
BIMI adds more branding to the inbox experience and there’s evidence it could help increase engagement metrics such as open rates. It could also serve as a sign that the email can be trusted.
That’s because any email that displays a BIMI logo has also been authenticated using DMARC. However, mailbox providers won’t show a BIMI logo unless you’re a DMARC policy of either p=quarantine or p=reject.
What does a DMARC record look like?
There’s more to a DMARC record than just the policy. Let’s take a closer look at the TXT record you’ll need to publish on your DNS server.
When you set up your DMARC policy and create a DNS record, there are up to 11 tags you may use. Only two of those are required: the v tag (version) and the p tag (policy). But you also want to use the “rua=” tag, because it defines the email addresses where receiving mail servers should send DMARC reports.
Here’s a quick explanation of all DMARC tags:
| v= | The version of DMARC used (DMARC1). |
| p= | The DMARC enforcement policy: none, quarantine, or reject. |
| rua= | A list of email addresses where DMARC aggregate reports are sent. |
| pct= | The percentage of messages that are subject to the enforcement policy. Default is pct=100. |
| aspf= | Defines the alignment mode for SPF, which could be strict or relaxed with pass/fail scenarios. |
| adkim= | Defines the alignment mode for DKIM, which could be strict or relaxed with pass/fail scenarios. |
| sp= | Represents different enforcement policies for subdomains. |
| ruf= | Lists email addresses for sending DMARC failure/forensic reports, which are more detailed than aggregate reports. |
| fo= | Indicates the options for creating a DMARC failure/forensic report. |
| rf= | Declares the forensic reporting format for message-specific failure reports. |
| ri= | Sets the interval for sending DMARC reports, which is defined in seconds but is usually 24 hours or more. |
A DMARC record with only the basics will look something like this:
v=DMARC1; p=reject; rua=mailto:dmarc-reports@yourcompany.com
The v and p tags must appear first. All other tags can appear in any order.
A somewhat more complex DMARC record might look like this:
v=DMARC1; p=quarantine; sp=quarantine; rua=mailto:dmarc-reports@yourcompany.com;
pct=100; aspf=s; adkim=s
If you’re pursuing BIMI implementation, it’s important to know about the values required for a couple of optional tags. As with your main DMARC policy, subdomain policies cannot be set to none (sp=none). Furthermore, the percentage tag must have a value of 100 (pct=100), which means all emails are subject to your DMARC policy.
How to publish a DMARC record
First, set up SPF and DKIM, if you haven’t done so already. Those should be running for at least 48 hours before you set up DMARC.
Then, go to your DNS hosting provider, and follow these steps:
- Add your DMARC record to your DNS by creating a new record.
- Use the TXT record type — this will likely be in a dropdown menu.
- Enter _DMARC in the Name or Host field.
- Enter the required tag value pairs (v= and p=) as well as any optional tag values needed.
- Save, or create, the DMARC record.
- Validate that the DMARC record has been set up correctly by running a DMARC Record Check.
If you start with a policy value of p=none during initial implementation and testing, you should eventually update it to p=quarantine or p=reject.
Setting up DMARC seems pretty simple on the surface, but it can get very technical. So, you may need to ask your IT department for help. There are also vendors that specialize in DMARC implementation.
For example, Red Sift is a cybersecurity company that offers OnDMARC, which is a service that helps out with many factors of email authentication, including BIMI as well as DKIM and SPF configuration. Other vendors who can help with DMARC include dmarcian and PowerDMARC.
The tools to improve email deliverability in 2024
DMARC is just one of several factors senders are thinking about this year thanks to the changes from Gmail and Yahoo. Research from Sinch Mailgun found the biggest benefits of prioritizing email deliverability are improved customer satisfaction and increased revenue.
If you’re ready to get serious about inbox placement, Mailgun Optimize is a complete deliverability suite. It includes reports that tell you if your authentication protocols are working properly. Plus, you’ll also find out if your emails are likely to land in spam, email validation tools, email previews, blocklist monitoring, and more.